Ever found yourself staring at a piece of software, a cryptic binary, or a protected application, and wondered how the digital shadows operate? How do skilled individuals unravel the intricate logic, bypass security measures, and extract knowledge from compiled code? This isn't magic; it's the disciplined art of Reverse Engineering. In this definitive dossier from Sectemple, we deconstruct this complex discipline into a clear, actionable 7-step roadmap designed for the aspiring ethical hacker and cybersecurity operative.
Advertencia Ética: La siguiente técnica debe ser utilizada únicamente en entornos controlados y con autorización explícita. Su uso malintencionado es ilegal y puede tener consecuencias legales graves.
MISSION INDEX
- Step 1: The Foundation - Understanding the Machine Code
- Step 2: Disassembly - Translating Binary to Assembly
- Step 3: Decompilation - Reconstructing Higher-Level Logic
- Step 4: Binary Analysis - The Hacker's Deep Dive
- Step 5: Navigating the Arsenal - Essential RE Tools
- Step 6: Malware Reverse Engineering - Unmasking the Threat
- Step 7: Exploit Development & Debugging - The Endgame
- Real-World Reverse Engineering Case Studies
- Comparative Analysis: RE Tools Showdown
- Frequently Asked Questions
- About The Cha0smagick
Step 1: The Foundation - Understanding the Machine Code
Before you can deconstruct, you must understand the fundamental language of computers: machine code. This is the raw, binary language that processors directly execute. Reverse engineering begins with grasping how instructions are encoded, how data is represented (integers, floats, strings), and the basic architecture of common processor families like x86 and ARM. Understanding memory layouts, registers, and the call stack is paramount. This foundational knowledge allows you to interpret the output of disassemblers and decompilers, making sense of the seemingly random sequences of bytes.
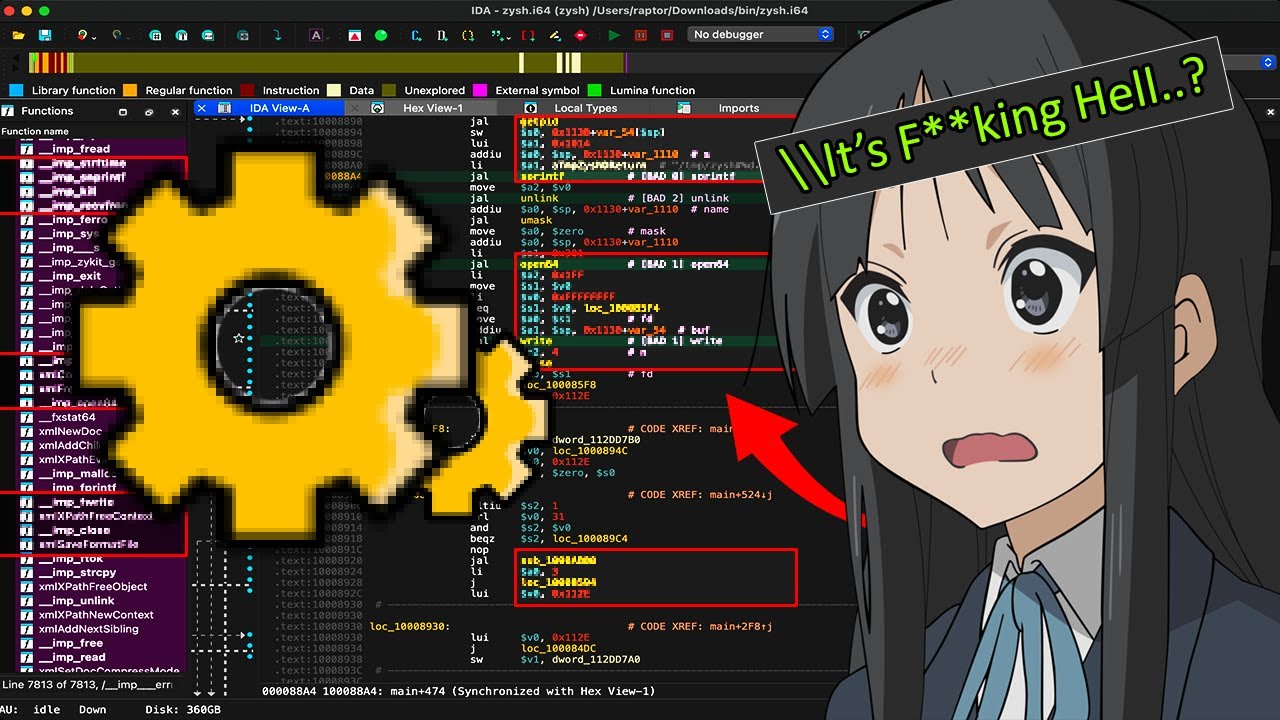
Step 2: Disassembly - Translating Binary to Assembly
Disassembly is the process of converting machine code back into assembly language. Assembly language is a low-level symbolic representation of machine code. While still complex, it's far more human-readable than raw binary. Disassemblers are tools that perform this translation. They analyze the executable file, identify instruction boundaries, and present the corresponding assembly mnemonics. This step is crucial for understanding the precise operations a program is performing at the processor level. Each instruction, though cryptic to the uninitiated, tells a story about data manipulation, control flow, and function calls.
"The art of reverse engineering is not about breaking things, but about understanding how they are built. It’s about seeing the blueprint where others only see a finished product."
Step 3: Decompilation - Reconstructing Higher-Level Logic
While disassembly provides a low-level view, decompilation attempts to reconstruct a higher-level representation, often resembling C or C++. Decompilers analyze the assembly code and apply heuristics to infer data structures, function calls, and control flow logic, presenting it in a more abstract form. While decompiled code is rarely a perfect replica of the original source code (information is lost during compilation), it significantly aids in understanding the program's overall functionality, algorithms, and intent. This is where complex logic starts to become comprehensible.
Step 4: Binary Analysis - The Hacker's Deep Dive
This is where the true detective work begins. Binary analysis involves meticulously examining the disassembled or decompiled code to identify vulnerabilities, hidden functionalities, or proprietary algorithms. This includes:
- Control Flow Analysis: Mapping out how the program executes, identifying loops, conditional branches, and function call chains.
- Data Flow Analysis: Tracing how data is processed, modified, and passed between variables and functions.
- Identifying Interesting Code Sections: Looking for cryptographic routines, network communication handlers, user input validation, and anti-debugging mechanisms.
- String and Resource Analysis: Extracting embedded strings, configuration data, and other resources that can provide clues about the program's purpose and potential weaknesses.
This methodical examination is what allows skilled analysts to find flaws that can be exploited or to understand the inner workings of complex software.
Step 5: Navigating the Arsenal - Essential RE Tools
A reverse engineer is only as good as their tools. Mastering a suite of powerful software is non-negotiable:
- Ghidra: A free, open-source software reverse engineering suite developed by the NSA. It offers powerful disassembly, decompilation, scripting, and analysis capabilities.
- IDA Pro: The industry standard for professional reverse engineering. It's a commercial tool known for its advanced features, extensive plugin support, and powerful decompiler.
- Radare2: A free, open-source command-line framework for reverse engineering and analyzing binaries. Highly scriptable and powerful, but with a steep learning curve.
- Binary Ninja: A modern, extensible reverse engineering platform with a focus on usability and a powerful intermediate language (IL) for analysis.
- Debuggers (x64dbg, GDB): Essential for dynamic analysis, allowing you to step through code execution, inspect memory and registers in real-time, and set breakpoints.
Understanding the strengths and weaknesses of each tool allows you to select the right one for the task at hand.
Step 6: Malware Reverse Engineering - Unmasking the Threat
One of the most critical applications of reverse engineering is in analyzing malicious software. This involves a specific methodology:
- Static Analysis: Examining the malware file without executing it, using tools like Ghidra or IDA Pro to understand its structure, identify imported functions, and look for suspicious strings or code patterns.
- Dynamic Analysis: Executing the malware in a controlled, isolated environment (a sandbox) to observe its behavior. This includes monitoring file system changes, registry modifications, network communications, and process interactions.
- Behavioral Analysis: Correlating static and dynamic findings to understand the malware's propagation methods, payload, command-and-control (C2) communication, and overall objective.
This process is vital for developing effective defenses against evolving cyber threats.
Step 7: Exploit Development & Debugging - The Endgame
With a deep understanding of a binary's inner workings and potential vulnerabilities, the next logical step for an ethical hacker is often exploit development. This involves crafting code that leverages a discovered vulnerability to achieve a specific outcome, such as gaining unauthorized access, escalating privileges, or executing arbitrary code. Debuggers are indispensable here, allowing the developer to precisely control program execution, inspect memory, and test exploit payloads in real-time. Mastering buffer overflows, use-after-free vulnerabilities, and other common exploit techniques builds upon the foundation laid by reverse engineering.
Real-World Reverse Engineering Case Studies
The theoretical steps are invaluable, but seeing them in action solidifies understanding. Consider the analysis of a proprietary video game's anti-cheat system. A reverse engineer might first disassemble the cheat protection module to understand its detection mechanisms. They would then use a debugger to step through the code, identifying specific memory locations or API calls that the anti-cheat monitors. By understanding how the anti-cheat validates game integrity, an ethical hacker can then develop methods to bypass or evade detection, not for malicious purposes, but to test the robustness of the security and provide feedback for improvement. Another example is analyzing a zero-day vulnerability in a widely used application. Researchers reverse engineer the vulnerable binary to understand the exact conditions that trigger the bug, enabling them to develop a patch or a signature for intrusion detection systems.
Comparative Analysis: RE Tools Showdown
While multiple tools exist, each has its niche:
- Ghidra vs. IDA Pro: Ghidra offers impressive power for free, making it accessible to everyone. IDA Pro, while costly, remains the gold standard for professional analysts due to its maturity, extensive plugin ecosystem, and highly refined decompiler.
- Radare2 vs. Binary Ninja: Radare2 is a powerhouse for command-line enthusiasts and scripters who thrive on customization. Binary Ninja offers a more modern, GUI-centric approach with a powerful intermediate language, appealing to those who prefer a visual workflow and robust API.
- Debuggers (x64dbg vs. GDB): x64dbg is a popular choice for Windows reversing, offering a user-friendly interface. GDB is the traditional debugger for Linux/Unix environments, incredibly powerful but often command-line driven.
The best approach often involves using a combination of these tools, leveraging their individual strengths.
Frequently Asked Questions
Q1: Is reverse engineering legal?
A1: The legality of reverse engineering often depends on jurisdiction, the terms of service of the software, and the purpose. In the US, for example, reverse engineering for interoperability or security research can be permissible under certain conditions (e.g., the DMCA exemption). However, reverse engineering for piracy or to circumvent copy protection is generally illegal. Always ensure you have the legal right and explicit permission to reverse engineer any software.
Q2: What is the most challenging aspect of reverse engineering?
A2: The most challenging aspect is often dealing with obfuscation techniques designed to hinder analysis, such as anti-disassembly, anti-debugging, and code packing. Overcoming these requires deep knowledge, creative problem-solving, and significant patience.
Q3: Do I need to be a programming genius to start reverse engineering?
A3: While advanced programming skills help, you don't need to be a genius. A solid understanding of at least one programming language (like C) and fundamental computer science concepts is crucial. Patience, logical thinking, and a willingness to learn are more important than innate genius.
Q4: How long does it take to become proficient in reverse engineering?
A4: Proficiency takes time and consistent practice. For some, a few months of dedicated study might lead to basic competency, while mastering the craft can take years, involving exposure to a wide variety of software and protection schemes.
About The Cha0smagick
I am The Cha0smagick, a seasoned digital operative with years spent navigating the intricate landscapes of technology. My expertise spans deep system analysis, ethical hacking, and digital forensics. Sectemple is my archive of intelligence—dossiers meticulously crafted to arm you with the knowledge to understand, defend, and innovate in the digital realm. Consider this your ongoing training ground.
Your Mission: Execute, Share, and Debate
Understanding reverse engineering is not just about acquiring knowledge; it's about developing a new way of thinking—a critical, analytical mindset essential for any serious cybersecurity professional. The power to deconstruct software is the power to truly understand its vulnerabilities and its strengths.
If this blueprint has illuminated the path for you, share it within your professional network. Knowledge is a tool, and this guide is designed to sharpen yours. Help fellow operatives level up their skills.
Do you know someone struggling to grasp the fundamentals of software analysis? Tag them in the comments below. A true operative ensures no one is left behind on the mission.
What specific software or protection mechanism do you want to see dissected in our next dossier? Your input shapes our operations. Demand it in the comments.
Mission Debriefing
The journey into reverse engineering is arduous but incredibly rewarding. By mastering these seven steps, you are not just learning a technique; you are adopting a mindset. You are becoming a digital architect, capable of understanding systems at their deepest level. Now, take this knowledge, apply it ethically, and continue your ascent.
For those looking to secure and diversify their digital assets, exploring robust platforms is key. Consider opening an account on Binance to explore a wide range of cryptocurrency services and trading opportunities.
Further Reading & Resources:
- Ghidra Official Website
- IDA Pro Official Website
- Radare2 GitHub Repository
- Binary Ninja Official Website
- Practical Malware Analysis Book
- More on Ethical Hacking Techniques
- Deep Dives into Malware Analysis
- Advanced Exploit Development Strategies
Trade on Binance: Sign up for Binance today!




